Hardware tokens versus tokenless 2FA
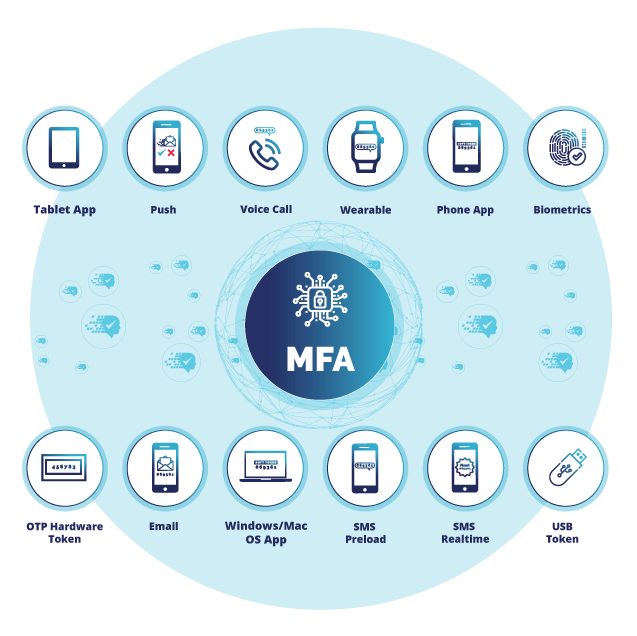
End user acceptance can make or break the implementation of any security system. When it comes to two-factor authentication, having a broad range of authenticators available to users is key to success.
Users and use cases can vary greatly, however the vast majority of requirements can be addressed via the deployment of a soft token 2FA app to user’s mobile phones. This type of app can serve to generate a 6-digt random one time passcode (OTP), used in conjunction with their username and password to securely logon. Alternatively the app can receive a secure push notification that simply requires the user to press accept and authorise the logon.
2FA apps are secure and user friendly, however in some instances where corporate mobile phones have not been supplied, users may prefer to use a traditional dedicated hardware token to authenticate. Hardware token deployments typically cost more than their virtual token counterparts, due to the procurement of additional hardware. There are however other hidden costs, in terms of the deployment and overall administration overhead of managing a physical token estate.
SecurEnvoy offers both software & hardware tokens as part of a wide range of authenticators allowing organisations to cater for all user requirements.
Read more about Tokenless 2FA – Authenticating without the need for a hardware token >